Telephone 1.5 is there, and it supports encryption.
UDP is probably the most widely used protocol for SIP. It is also used by default in Telephone. If you haven’t changed SIP transport in settings, UDP is used. Some public SIP providers or company servers may also work with TCP, but UDP still seems to be the default.
Neither UDP nor TCP transport provides encryption. The communication between the phone and the SIP server happens in the clear. One way of solving this problem is to use a VPN connection between your computer and your SIP provider or company network.
Such remote access VPN is typical for remote workers in a company. But it is not typical for a public SIP provider to offer access to their servers via VPN.
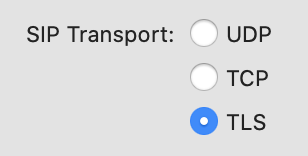
TLS as SIP transport
There is another standard transport protocol. It is called TLS, and it supports encryption. It is the same TLS that is widely used on the web where you can recognize it by a padlock icon in the browser or https scheme in the site address.
The same TLS transport that is used on the web can also be used for SIP. Of course, both the phone and the SIP server have to support it. In this update, Telephone has gotten support for it, so you might want to ask your SIP provider or IT service about the support on the server.
When TLS is used, the server presents its cryptographic certificate to the phone. The phone allows the connection only if the server’s certificate has been issued by an authority that is trusted by the phone. Telephone has a built-in list of trusted public certificate authorities in a similar way as an operating system or a web browser does.
This means that for TLS to work, the server must get a certificate from one of the public certificate authorities. Self-signed certificates would not currently work.
SRTP for voice
In SIP VoIP, the SIP protocol itself is only part of the story. It is responsible for establishing calls and controlling the call flow, but it doesn’t transmit voice. For the voice, another protocol called RTP is used.
By default, the voice transmission isn’t encrypted either. As with SIP above, one way of solving this problem is to use a VPN tunnel. In a VPN tunnel, all traffic is usually encrypted, being it SIP or RTP.
However, there is a specially designed protocol for encrypted voice transmission called SRTP, and Telephone now also supports it.
TLS and SRTP together
To negotiate its encryption keys, SRTP relies on SIP. To make voice transmission with SRTP secure, secure transport has to be used for SIP. That’s why SRTP for voice is usually used together with TLS for SIP.
In Telephone, when TLS is chosen as a SIP transport, SRTP is automatically required instead of plain RTP. If the server doesn’t support SRTP, the call will not succeed. This way you may be sure that when TLS is selected, your voice between Telephone and the SIP server will also be encrypted.
No end-to-end encryption
You need to keep in mind that the standard encryption protocols above don’t give you end-to-end encryption between two phones. In SIP telephony, your phone connects to a SIP server. And that in turn connects either to the server of your conversation partner or to their phone directly. There’s no guarantee of what happens to the network traffic after the first server decrypts it. And when a normal phone number is called, there is no guarantee of encryption in the traditional phone network.
However, encryption between the phone and your SIP server alone is also important. You often don’t have a choice but to trust your SIP server. Otherwise, you wouldn’t have chosen this provider in the first place. But it is a good idea not to trust the network between you and the server and to encrypt all communications with it.